Nezha server over Argo tunnel
INFO
This community project is not yet compatible with the V1 version. This page is kept for historical reference; check the upstream repository status before deploying it, and do not apply it directly to the current Nezha version.
Contributors:
GitHub project: Argo-Nezha-Service-Container
Catalog
- Project Features
- How to get Argo authentication: json or token
- Variables to be used
- PaaS Deployment Example
- VPS Deployment Method 1 --- docker
- VPS Deployment Method 2 --- hosts
- Client Access
- SSH Access
- Manual Backup data
- Auto Restore Backup
- Manual Restore Backup
- Migrating data
- Main Directory Files and Descriptions
- Acknowledgment of articles and projects by the following authors
- Disclaimer
Project Features.
- Wider scope of application --- As long as there is a network connection, Nezha server can be installed, such as LXC, OpenVZ VPS, Nas Virtual Machine, Container PaaS, etc.
- Argo tunnel breaks through the restriction of requiring a public network portal --- The traditional Nezha requires two public network ports, one for panel visiting and the other for client reporting, this project uses Cloudflare Argo tunnels and uses intranet tunneling.
- IPv4 / v6 with higher flexibility --- The traditional Nezha needs to deal with IPv4/v6 compatibility between server and client, and also needs to resolve mismatches through tools such as warp. However, this project does not need to consider these issues at all, and can be docked arbitrarily, which is much more convenient and easy!
- One Argo tunnel for multiple domains and protocols --- Create an intranet-penetrating Argo tunnel for three domains (hostname) and protocols, which can be used for panel access (http), client reporting (tcp) and ssh (optional).
- GrpcWebProxy reverse proxy gRPC data port --- with a certificate for tls termination, then Argo's tunnel configuration with https service pointing to this reverse proxy, enable http2 back to the source, grpc(nezha)->GrpcWebProxy->h2(argo)->cf cdn edge->agent
- Daily automatic backup --- every day at 04:00 BST, the entire Nezha panel folder is automatically backed up to a designated private github repository, including panel themes, panel settings, probe data and tunnel information, the backup retains nearly 5 days of data; the content is so important that it must be placed in the private repository.
- Automatic daily panel update -- the latest official panel version is automatically detected every day at 4:00 BST, and updated when there is an upgrade.
- Manual/automatic restore backup --- check the content of online restore file once a minute, and restore immediately when there is any update.
- Default built-in local probes --- can easily monitor their own server information
- More secure data --- Argo Tunnel uses TLS encrypted communication to securely transmit application traffic to the Cloudflare network, improving application security and reliability. In addition, Argo Tunnel protects against network threats such as IP leaks and DDoS attacks.
Prepare variables to be used
- Visit the Cloudflare website, select the domain name you want to use, and turn on the
networkoption to turn thegRPCswitch on.
- Get github authentication license: https://github.com/settings/applications/new
Add https:// to the beginning of the panel's domain name and /oauth2/callback to the end of the callback address.
- Get a PAT (Personal Access Token) for github: https://github.com/settings/tokens/new
- Create a private github repository for backups: https://github.com/new
How to get Argo authentication: json or token
Argo tunnel authentication methods include json and token, use one of the two methods. The former is recommended because the script will handle all the Argo tunnel parameters and paths, while the latter needs to be set manually on the Cloudflare website and is prone to errors.
(Methods 1 - Json):
Easily get Argo tunnel json information through Cloudflare Json Generation Network: https://fscarmen.cloudflare.now.cc
(Methods 2 - Token): Manually generate Argo tunnel token information via Cloudflare website.
Go to the cf website: https://dash.cloudflare.com/
- Go to zero trust and generate token tunnel and message.
- The data path 443/https is proto.
- ssh path 22/ssh for < client id >.
PaaS Deployment Example
Image fscarmen/argo-nezha:latest, supports amd64 and arm64 architectures.
Variables used
| Variable Name | Required | Remarks |
|---|---|---|
| GH_USER | Yes | github username for panel admin authorization |
| GH_CLIENTID | yes | apply on github |
| GH_CLIENTSECRET | yes | apply on github |
| GH_BACKUP_USER | No | The github username for backing up Nezha's server-side database on github, if not filled in, it is the same as the account GH_USER for panel management authorization |
| GH_REPO | No | The github repository for backing up Nezha's server-side database files on github |
| GH_EMAIL | No | github's mailbox for git push backups to remote repositories |
| GH_PAT | No | github's PAT |
| ARGO_AUTH | Yes | Argo Json from https://fscarmen.cloudflare.now.cc Argo token from Cloudflare official website |
| ARGO_DOMAIN | Yes | Argo domain |
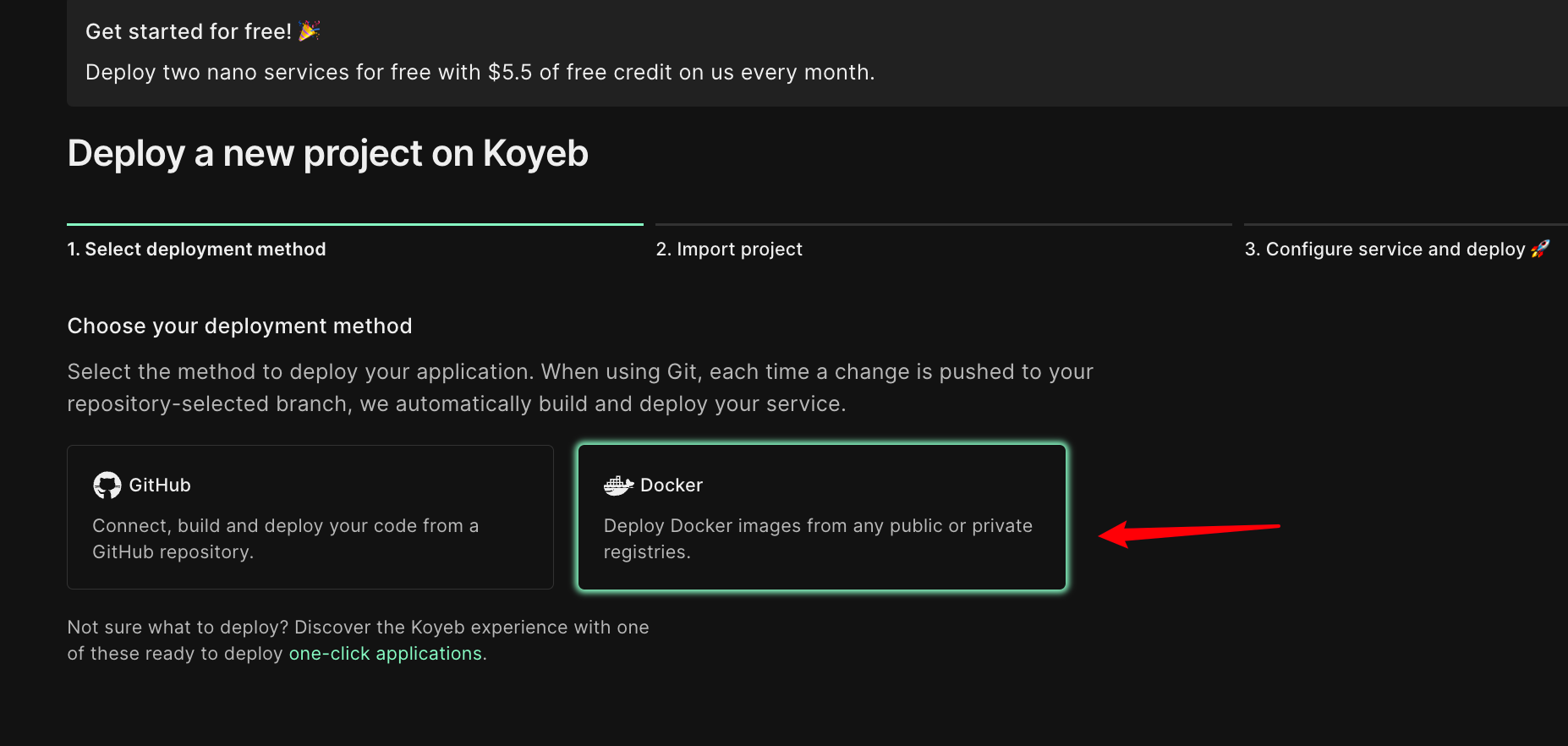
Koyeb
VPS Deployment Method 1 --- docker
- Note: ARGO_DOMAIN= must be followed by single quotes, which cannot be removed.
- If the VPS is IPv6 only, please install WARP IPv4 or dual-stack first: https://github.com/fscarmen/warp
- The backup directory is the dashboard folder in the current path.
docker deployment
docker run -dit \
--name nezha_dashboard \
--pull always \
--restart always \
-e GH_USER=<fill in github username> \
-e GH_EMAIL=<fill in github email> \
-e GH_PAT=<fill in the obtained> \
-e GH_REPO=<fill in customized> \
-e GH_CLIENTID=<fill in acquired> \
-e GH_CLIENTSECRET=<fill in acquired> \
-e ARGO_AUTH='<Fill in the fetched Argo json or token>' \
-e ARGO_DOMAIN=<fill in customized> \
-e GH_BACKUP_USER=<If it is consistent with GH_USER, you can leave it blank> \
fscarmen/argo-nezhadocker-compose deployment
version: '3.8'
services.
argo-nezha.
image: fscarmen/argo-nezha
--pull always
container_name: nezha_dashboard
restart: always
environment:
- GH_USER=<fill in github username>
- GH_EMAIL=<fill in your github email>
- GH_PAT=<<fill in obtained>
- GH_REPO=<fill in customized>
- GH_CLIENTID=<fill in obtained>
- GH_CLIENTSECRET=<fill in fetched>
- ARGO_AUTH='<Fill in the fetched Argo json or token>'
- ARGO_DOMAIN=<fill in customized>
- GH_BACKUP_USER=<If it is consistent with GH_USER, you can leave it blank>VPS Deployment Method 2 --- hosts
bash <(wget -qO- https://raw.githubusercontent.com/fscarmen2/Argo-Nezha-Service-Container/main/dashboard.sh)Client Access
Transfer via gRPC, no additional configuration required. Use the installation method given in the panel, for example
curl -L https://raw.githubusercontent.com/nezhahq/scripts/main/install_en.sh -o nezha.sh && chmod +x nezha.sh && sudo ./nezha.sh install_agent data.seales.nom.za 443 eAxO9IF519fKFODlW0 --tlsSSH access
- Take macOS + WindTerm as an example, and other SSH tools depending on the one used, combined with the official documentation: https://developers.cloudflare.com/cloudflare-one/connections/connect-apps/use_cases/ssh /#2-connect-as-a-user
- Official cloudflared download: https://github.com/cloudflare/cloudflared/releases
- The following are examples of input commands. SSH user: root, SSH password:<GH_CLIENTSECRET>
<filepath>/cloudflared access ssh --hostname ssh.seals.nom.za/<GH_CLIENTID>Manually backing up your data
Method 1: Change the contents of the README.md file in the Github backup repository to backup
Method 2: After ssh, run /dashboard/backup.sh for container version; /opt/nezha/dashboard/backup.sh for VPS host version.
Automatically restore backups
- Change the name of the file to be restored to
README.mdin the github backup repository, the timer service will check for updates every minute and record the last synchronized filename in the local/dbfileto compare with the online file content.
The following is an example of restoring a file with the name dashboard-2023-04-23-13:08:37.tar.gz.
! image
Manually restore the backup
- ssh into the container and run, tar.gz filename from the github backup repository, format: dashboard-2023-04-22-21:42:10.tar.gz
bash /dashboard/restore.sh <filename>
Migrating data
- Backup the
/dashboardfolder of the original Nezha and zip it up todashboard.tar.gzfile.
tar czvf dashboard.tar.gz /dashboard- Download the file and put it into a private repository, the name of the repository should be exactly the same as <GH_REPO>, and edit the contents of README.md of the repository to
dashboard.tar.gz. - Deploy the new Nezha in this project, and fill in the variables completely. After the deployment is done, the auto-restore script will check every minute, and will restore automatically if it finds any new content, the whole process will take about 3 minutes.
Main catalog files and descriptions
/dashboard/
|-- app # Nezha panel main program
|-- argo.json # Argo tunnel json file, which records information about using the tunnel.
|-- argo.yml # Argo tunnel yml file, used for streaming web, gRPC and ssh protocols under a single tunnel with different domains.
|-- backup.sh # Backup data scripts
|-- restore.sh # Restore backup scripts
|-- dbfile # Record the name of the latest restore or backup file
|-- resource # Folders of information on panel themes, languages, flags, etc.
|-- data
| |-- config.yaml # Configuration for the Nezha panel, e.g. Github OAuth2 / gRPC domain / port / TLS enabled or not.
| `-- sqlite.db # SQLite database file that records all severs and cron settings for the panel.
|-- entrypoint.sh # The main script, which is executed after the container is run.
|-- nezha.csr # SSL/TLS certificate signing request
|-- nezha.key # Private key information for SSL/TLS certificate.
|-- nezha.pem # SSL/TLS certificate file.
|-- cloudflared # Cloudflare Argo tunnel main program.
|-- grpcwebproxy # gRPC reverse proxy main program.
`-- nezha-agent # Nezha client, used to monitor the localhost.Acknowledgements for articles and projects by
- Robin, an enthusiastic sunrise crowd, for discussing the relationship between Nezha's server and client, which led to the birth of this project.
- Nezha website: https://nezha.wiki/ , TG Group: https://t.me/nezhamonitoring
- Common Poverty International Old Chinese Medicine: http://solitud.es/
- Akkia's Blog: https://blog.akkia.moe/
- Ayaka's Blog: https://blog.萝莉.org/
- HiFeng's Blog: https://www.hicairo.com/
- Intranet Penetration with Cloudflare Tunnel: https://blog.outv.im/2021/cloudflared-tunnel/
- How to add your own Runner host to GitHub Actions: https://cloud.tencent.com/developer/article/1756690
- github self-hosted runner addition and startup: https://blog.csdn.net/sinat_32188225/article/details/125978331
- How to export a file from a Docker image: https://www.pkslow.com/archives/extract-files-from-docker-image
- grpcwebproxy: https://github.com/improbable-eng/grpc-web/tree/master/go/grpcwebproxy
- Applexad's binary of Nezha's officially dashboard: https://github.com/applexad/nezha-binary-build
Disclaimer
- This program is only for learning and understanding, non-profit purposes, please delete within 24 hours after downloading, not for any commercial purposes, text, data and images are copyrighted, if reproduced must indicate the source.
- Use of this program is subject to the deployment disclaimer. Use of this program must follow the deployment of the server location, the country and the user's country laws and regulations, the author of the program is not responsible for any misconduct of the user.
